The 13th International Conference on Provable and Practical Security (ProvSec 2019)
Cairns, Australia, 1 - 4 October 2019
Cairns, Australia, 1 - 4 October 2019
Provable security is an essential tool for analyzing security of modern cryptographic primitives. The research community has witnessed the great contributions that the provable security methodology made to the analysis of cryptographic schemes and protocols. Nowadays cryptographic primitives without a rigorous "proof" cannot be regarded as sound. Also, the methodology has been used to discover security flaws in the cryptographic schemes and protocols, which were considered seemingly secure without formal analysis. On the one hand, provable security provides confidence in using cryptographic schemes and protocols for various real-world applications, but on the other hand, schemes with provable security are sometimes not efficient enough to be used in practice, and correctness of the proofs may be difficult to verify.
Therefore, this year we decide to enrich the scope of this conference, by adding “Practical Security” into the theme. The new theme can bring together researchers and practitioners to provide a confluence of new practical cyber security technologies, including their applications and their integration with IT systems in various industrial sectors.
Full proceedings are available.
Day 0 (1/10/2019) | Guest Arriving |
Day 1 (2/10/2019) | |
17:00 - 19:00 | Registration and Welcome Reception (Salt House: https://salthouse.com.au/) |
Day 2 (3/10/2019) | |
9:00 - 9:20 | Opening (Session Chair: Joseph Liu) |
9:20 - 10:20 | Keynote: Open problems and challenges in post-quantum cryptography (Session Chair: Ron Steinfeld) Professor Steven Galbraith, University of Auckland, New Zealand |
10:20 - 10:50 | Coffee Break |
10:50 - 12:30 | Lattice-Based Cryptography (Session Chair: Huaxiong Wang) A Practical Lattice-Based Sequential Aggregate Signature Zhipeng Wang (Beihang University, China) and Qianhong Wu (Beihang University, China) Identity-Concealed Authenticated Encryption from Ideal Lattices Chao Liu (Shandong University, China), Zhongxiang Zheng (Tsinghua University, China), Keting Jia (Tsinghua University, China) and Limin Tao (Space star technology, China) A Lattice-Based Anonymous Distributed E-Cash from Bitcoin Zeming Lu (Harbin Institute of Technology, Shenzhen, China), Zoe L. Jiang (Harbin Institute of Technology, Shenzhen, China), Yulin Wu (Harbin Institute of Technology, Shenzhen, China), Xuan Wang (Harbin Institute of Technology, Shenzhen, China), Yantao Zhong (Shenzhen Network Security Testing Technology, China) Lattice-based IBE with equality test in standard model Dung Hoang Duong (University of Wollongong, Australia), Huy Quoc Le (Kyushu University, Japan), Partha Sarathi Roy (University of Wollongong, Australia), and Willy Susilo (University of Wollongong, Australia) |
12:30 - 13:30 | Lunch |
13:30 - 14:20 | Attack (Session Chair: Steven Galbraith) Solving ECDLP via List Decoding Fangguo Zhang (Sun Yat-sen University, China) and Shengli Liu (Shanghai Jiao Tong University, China) Improved Cryptanalysis of the KMOV Elliptic Curve Cryptosystem Abderrahmane Nitaj (University of Caen Normandie, France), Willy Susilo (University of Wollongong, Australia) and Joseph Tonien (University of Wollongong, Australia) |
14:20 - 15:05 | Model and Framework (Session Chair: Bin Yu) On-demand Privacy Preservation for Cost-Efficient Edge Intelligence Model Training(Short) Zhi Zhou (Sun Yat-sen University, China) and Xu Chen (Sun Yat-sen University, China) A Hidden Markov Model-Based Method for Virtual Machine Anomaly Detection(Short) Chaochen Shi (China Mobile, China) and Jiangshan Yu (Monash University, Australia) A Coin-Free Oracle-Based Augmented Black Box Framework(Short) Kyosuke Yamashita (Kyoto University, Japan), Masayuki Abe (NTT, Japan) and Mehdi Tibouchi (NTT, Japan) |
15:05 - 15: 35 | Coffee Break |
15:35 - 17:15 | Searchable and Verifiable Encryption (Session Chair: Shabnam Kasra) Plaintext-Verifiably-Checkable Encryption Sha Ma (South China Agricultural University, China), Qiong Huang (South China Agricultural University, China), Ximing Li (South China Agricultural University, China) and Meiyan Xiao (South China Agricultural University, China) FSPVDsse: A Forward Secure Publicly Verifiable Dynamic SSE scheme Laltu Sardar (Indian Statistical Institute, Kolkata, India) and Sushmita Ruj (Indian Statistical Institute, Kolkata, India) Space-Efficient and Secure Substring Searchable Symmetric Encryption Using an Improved DAWG Hiroaki Yamamoto (Shinshu University, Japan), Yoshihiro Wachi (NTT, Japan) and Hiroshi Fujiwara (Shinshu University, Japan) Towards enhanced security for Certificateless Public-key Authenticated Encryption with Keyword Search Xueqiao Liu (University of Wollongong, Australia), Hongbo Li (South China Agricultural University, China), Guomin Yang (University of Wollongong, Australia), Willy Susilo (University of Wollongong, Australia), Joseph Tonien (University of Wollongong, Australia) and Qiong Huang (South China Agricultural University, China) |
Day 3 (4/10/2019) | |
9:30 - 10:30 | Keynote: Hash Proof System and Public-Key Encryption Secure against Chosen-Ciphtertext Attacks (Session Chair: Tsz Hon Yuen) Professor Shengli Liu, Shanghai Jiao Tong University, China |
10:30 - 11:00 | Coffee Break |
11:00 - 12:15 | Payment and Voting (Session Chair: Jiangshan Yu) A critique of game-based definitions of receipt-freeness for voting Ashley Fraser (Royal Holloway, University of London, UK), Elizabeth Quaglia (Royal Holloway, University of London, UK) and Ben Smyth (University of Luxembourg, Luxembourg) A centralized digital currency system with rich functions Haibo Tian (Sun Yat-sen University, China), Peiran Luo (Sun Yat-sen University, China) and Yinxue Su (Sun Yat-sen University, China) Chameleon Hash Time-Lock Contract for Privacy Preserving Payment Channel Networks Bin Yu (Monash University, Australia), Shabnam Kasra (Monash University, Australia), Amin Sakzad (Monash University, Australia) and Surya Nepal (CSIRO Data61, Australia) |
12:15 - 13:30 | Lunch |
13:30 - 14:35 | Cryptographic Primitive (I) (Session Chair: Man Ho Au) Provably Secure Proactive Secret Sharing Without the Adjacent Assumption Zhe Xia (Wuhan University of Technology, China), Bo Yang (Shaanxi Normal University, China), Yanwei Zhou (Shaanxi Normal University, China), Mingwu Zhang (Hubei University of Technology, China), Hua Shen (Hubei University of Technology, China) and Yi Mu (Fujian Normal University, China) History-Free Sequential Aggregate MAC Revisited Shoichi Hirose (University of Fukui, Japan) and Junji Shikata (Yokohama National University, Japan) Secure Online/Offline Attribute-based Encryption for IOT Users in Cloud Computing(Short) Xiang Li (National Huaqiao University, China), Hui Tian (National Huaqiao University, China) and Jianting Ning (National University of Singapore, Singapore) |
14:35 - 15:15 | Privacy Protocol (Session Chair: Shifeng Sun) An Efficient Conditional Privacy-Preserving Authentication Scheme for Vehicular Ad Hoc Networks Using Online/Offline Certificateless Aggregate Signature Kang Li (The Hong Kong Polytechnic University, Hong Kong, China), Man Ho Au (The Hong Kong Polytechnic University, Hong Kong, China), Wang Hei Ho (The Hong Kong Polytechnic University, Hong Kong, China) and Yi Lei Wang (The Hong Kong Polytechnic University, Hong Kong, China) TumbleBit++: A Comprehensive Privacy Protocol Providing Anonymity and Amount-invisibility(Short) Yi Liu (Shanghai Jiao Tong University, China), Zhen Liu (Shanghai Jiao Tong University, China), Yu Long (Shanghai Jiao Tong University, China), Zhiqiang Liu (Shanghai Jiao Tong University, China), Dawu Gu (Shanghai Jiao Tong University, China), Fei Huan (Shanghai Jiao Tong University, China) and Yanxue Jia (Shanghai Jiao Tong University, China) |
15:15 - 15:45 | Coffee Break |
15:45 - 16:50 | Cryptographic Primitive (II) (Session Chair: Cong Zuo)
Hierarchical Functional Signcryption: Notion and Construction Dongxue Pan (China Academy of Sciences, China), Bei Liang (Chalmers University of Technology, Sweden), Hongda Li (China Academy of Sciences, China) and Peifang Ni (China Academy of Sciences, China) Password-based Authenticated Key Exchange from Standard Isogeny Assumptions Shintaro Terada (Ibaraki University, Japan) and Kazuki Yoneyama (Ibaraki University, Japan) One-Round Authenticated Group Key Exchange from Isogenies(Short) Atsushi Fujioka (Kanagawa University, Japan), Katsuyuki Takashima (Mitsubishi Electric, Japan) and Kazuki Yoneyama (Ibaraki University, Japan) |
16:50 - 17:00 | Closing and ProvSec 2020 Introduction |
18:00 - 21:00 | Banquet (Dundee’s Restaurant Waterfront: https://www.dundees.com.au/) |
Full paper: 25 min. Short paper: 15 min

Professor Steven Galbraith, Head, Mathematics Department, University of Auckland, New Zealand
Biography: Professor Steven Galbraith has a Bachelor of Computing and Mathematical Sciences from the University of Waikato (NZ), a Master of Science from Georgia Institute of Technology (USA) and a doctorate from Oxford University (UK). He held research positions at Royal Holloway University of London (UK), University of Waterloo (Canada), the Institute for Experimental Mathematics, Essen (Germany) and the University of Bristol (UK).He was a lecturer from 2001 to 2009 in the Mathematics Department of Royal Holloway University of London (UK), and was made full professor there in 2008. He moved to the University of Auckland in 2009 and is currently the Head of the Mathematics Department. His research is in computational number theory, computational algebraic geometry and applications in public key cryptography. Currently his main research focus is post-quantum cryptography. He is an international leader in the mathematics of public key cryptography and wrote a large book with this title that was published in 2012 by Cambridge University Press. He has supervised around 12 PhD theses and 20 Masters theses. He serves on the Editorial board of the journal "Designs, Codes and Cryptography" and is the program co-chair of ASIACRYPT in 2018 and 2019.
Title: Open problems and challenges in post-quantum cryptography
Abstract: If a large-scale quantum computer can be built that can run Shor's algorithm then many commonly used public key cryptosystems, such as RSA and elliptic curve cryptography, will be insecure. This motivates the search for public key cryptosystems that resist attack using quantum computers. In 2016 NIST announced a post-quantum cryptography standardization plan, and this has stimulated a large amount of research. The talk will give an overview of the field. I will then briefly discuss lattice and isogeny cryptography, and will mention some recent research and open problems.

Professor Shengli Liu, Department of Computer Science and Engineering, Shanghai Jiao Tong University, China
Biography: Shengli Liu got her B.S., M.S. and Ph.D degrees from Xidian University in 1995, 1998, 2000 respectively. She got another Ph..D degree from Technische Universiteit Eindhoven on Feb, 2002. She joined Department of Computer Science and Engineering, Shanghai Jiao Tong University in 2002 and now is a tenure- professor. Her research interests include public key cryptography and fuzzy extraction. In recent years, she has published a dozen of papers on top cryptographic conference like Crypto, EuroCrypt, AsiaCrypt, and PKC.
Title: Hash Proof System and Public-Key Encryption Secure against Chosen-Ciphtertext Attacks
Abstract: Hash Proof System (HPS) provides an efficient way of constructing CCA secure public-key encryption (PKE), as shown by Cramer and Shoup. However, the security reduction is not tight in the scenario of multiple challenge ciphertexts and multi-users. We introduce the concept of quasi-adaptive hash proof system (QAHPS), where the projection key is allowed to depend on the specific language for which hash values are computed. We formalize ardency for QAHPS by defining two statistical properties, including <L0, L1>-universal and <L0, L1>-key-switching. Then we provide a generic approach to tightly CCA-secure PKE from ardent QAHPS. We also show how to extend this approach to achieve tightly leakage-resilient CCA-security.
Authors are invited to submit full papers presenting new research results related to information security technologies and applications. Areas of interest include, but are not limited to:
* Asymmetric provably secure cryptography
* Symmetric cryptographic primitives
* Lattice-based security reductions
* Leakage-resilient cryptography
* Privacy and anonymity technologies
* Secure cryptographic protocols and applications
* Security notions, approaches, and paradigms
* Steganography and steganalysis
* Blockchain and Cryptocurrency
* IoT Security
* Mobile security
* Cloud security
* Access control
* Privacy enhanced technology
* Viruses and malware
* Software security
* Database security
* Web security
* Operating system security
* Intrusion detection
* Big data security and privacy
* Biometric Security
* Network security
* Formal methods for security
* Digital forensics
* Security for critical infrastructures
* Embedded systems security
* Lightweight security
* Smart grid security
* Cyber-physical security
Instructions for Authors
Submissions must be at most 16 pages excluding the bibliography, well-marked appendices, and supplementary material, and using the Springer LNCS format. Details on the Springer LNCS format can be obtained here. Authors should not change the font or the margins of the LNCS format. There is no page limit on the appendices and supplementary material. Note that reviewers are not required to read the appendices or any supplementary material. It is strongly encouraged that submissions are processed in LaTeX. All submissions must have page numbers.
All submissions will be blind-refereed and thus must be anonymous, with no author names, affiliations, acknowledgments, or obvious references. Submissions must be submitted electronically in PDF format. Submissions must not substantially duplicate work that any of the authors has published elsewhere or has submitted in parallel to a journal or any other conference/workshop that has proceedings. Accepted submissions may not appear in any other conference or workshop that has proceedings. Submissions not meeting these guidelines risk rejection without consideration of their merits.
Submission link:
https://easychair.org/conferences/?conf=provsec2019
Important Dates:
Paper Submission: 14 June 2019
Extended Submission Deadline: 24 June 2019 (Any Time on Earth), Authors are allowed to modify their submission until 26 June 2019 (Any Time on Earth)
Notification: 15 July 2019
Conference: 1 – 4 October 2019
Proceedings including all accepted papers will be published in LNCS and will be available at the conference.
Organising Committee
General Co-Chairs
Joseph K. Liu, Monash University, Australia
Wei Xiang, James Cook University, Australia
Program Co-Chairs
Ron Steinfeld, Monash University, Australia
Tsz Hon Yuen, University of Hong Kong, Hong Kong
Publication Chair
Jiangshan Yu, Monash University, Australia
Publicity Co-Chairs
Xingliang Yuan, Monash University, Australia
Yu Wang, Guangzhou University, China
Technical Program Committee Members
Elena Andreeva, Katholieke Universiteit Leuven, Belgium
Man Ho Au, The Hong Kong Polytechnic University, Hong Kong
Joonsang Baek, University of Wollongong, Australia
Donghoon Chang, NIST, US
Xiaofeng Chen, Xidian University, China
Jie Chen, East China Normal University, China
Liqun Chen, University of Surrey, UK
Cheng-Kang Chu, Huawei, Singapore
Bernardo David, The University of Tokyo, Japan
Keita Emura, National Institute of Information and Communications Technology, Japan
Zekeriya Erkin, Delft University of Technology, Netherlands
Jinguang Han, Queen's University Belfast, UK
Xinyi Huang, Fujian Normal University, China
Ryo Kikuchi, NTT, Japan
Jongkil Kim, University of Wollongong, Australia
Veronika Kuchta, Monash University, Australia
Jianchang Lai, University of Wollongong, Australia
Hyung Tae Lee, Chonbuk National University, Korea
Jooyoung Lee, Korea Advanced Institute of Science and Technology, Korea
Kaitai Liang, University of Surrey, UK
Joseph Liu, Monash University, Australia
Rongxing Lu, University of New Brunswick, Canada
Daniel Xiapu Luo, The Hong Kong Polytechnic University, Hong Kong
Siqi Ma, CSIRO, Australia
Bernardo Magri, Aarhus University, Denmark
Barbara Masucci, University of Salerno, Italy
Bart Mennink, Radboud University, Netherlands
Chris Mitchell, Royal Holloway, University of London, UK
Kirill Morozov, University of North Texas, US
Abderrahmane Nitaj, LMNO, Université de caen, France
Raphael Phan, Monash University Malaysia, Malaysia
Josef Pieprzyk, CSIRO, Australia
Kouichi Sakurai, Kyushu University, Japan
Ron Steinfeld, Monash University, Australia
Rainer Steinwandt, Florida Atlantic University, US
Chunhua Su, University of Aizu, Japan
Shi-Feng Sun, Monash University, Australia
Willy Susilo, University of Wollongong, Australia
Katsuyuki Takashima, Mitsubishi Electric, Japan
Atsushi Takayasu, The University of Tokyo, Japan
Qiang Tang, New Jersey Institute of Technology, US
Dongvu Tonien, University of Wollongong, Australia
Damien Vergnaud, Université Pierre et Marie Curie / Institut Universitaire de France, France
Sheng Wen, Swinburne University of Technology, Australia
Qianhong Wu, Beihang University, China
Chung-Huang Yang, National Kaohsiung Normal University, Taiwan
Guomin Yang, University of Wollongong, Australia
Wun She Yap, Universiti Tunku Abdul Rahman, Malaysia
Xun Yi, RMIT University, Australia
Yong Yu, Shaanxi Normal University, China
Xingliang Yuan, Monash University, Australia
Tsz Hon Yuen, The University of Hong Kong, Hong Kong
Aaram Yun, University of Minnesota, US
Full registration payment is required by 1 August 2019 for EACH accepted paper. This deadline will be strictly enforced. Failure to pay the registration fee by 1 August 2019 will result in the exclusion of the papers from the Conference Proceedings.
| Registration Fee (in Australian Dollar) | By 1 August 2019 | After 1 August 2019 |
|---|---|---|
| Full Registration | A$1100 | A$1200 |
| Student Registration | A$800 | A$800 |
| Extra Page (per page) | A$50 | A$50 |
| Additional Conference Banquet Ticket (per person) | A$150 | A$150 |
Both types of registration include: full attendance of the conference, conference proceedings, welcome reception, conference banquet, morning teas, afternoon teas and lunches.
To be qualified for student registration, you must be currently enrolled as a full time student in a university or an institution. A scanned copy of your valid student ID card must be sent to the conference secretary (abby.xu@insightek.com.au). The student status will be verified.
Please note that if you are the only author registered for an accepted paper, you should choose Full Registration (instead of Student Registration) even though you are a student.
If extra pages are required, payment of $50 per extra page needs to be made together with the conference registration fee.
A conference banquet ticket is included in both full registration and student registration. Additional conference banquet tickets are available for purchase at the cost of A$150 per person. Payment needs to be made together with the conference registration fee.
If you need an invitation letter, please contact the conference secretary (abby.xu@insightek.com.au) AFTER you complete the registration. The invitation letter can be issued once your registration payment is received.
Registration for the conference cannot be canceled. There is no refund of registration fees.
Please click the following link to complete your registration.
ProvSec2019 Registration System
Payment via credit card or PayPal can be made directly in the registration system.
Payment via bank transfer are accepted at the following account. For participants who want to pay by bank transfer, please send the payment AS SOON AS POSSIBLE as it takes some time to process the payment.
| Account name | Insightek |
| Bank Name | Commonwealth Bank of Australia |
| Address of Insightek | 2B Service Road, Blackburn, VIC 3130, Australia |
| SWIFT code | CTBAAU2S |
| BSB/Account No | 063182 10939649 |
After the bank transfer is completed, please send a scanned copy of the bank transfer transaction receipt to the conference secretary (abby.xu@insightek.com.au) with your name and paper ID. We will confirm your registration once we receive the payment and the scanned transaction receipt.
Conference Venue
James Cook University, Cairns Campus, Lecture Hall in the Cairns Institute (Building D3 in the map below):
https://maps.jcu.edu.au/pdfs/jcu_cns_map.pdf
Note that the conference reception and conference dinner will be held in the Cairns CBD instead of the campus.
For those who drive to the venue, there is a free car park (P2 in the map) nearby:
https://maps.jcu.edu.au/pdfs/jcu_cns_trns_map.pdf
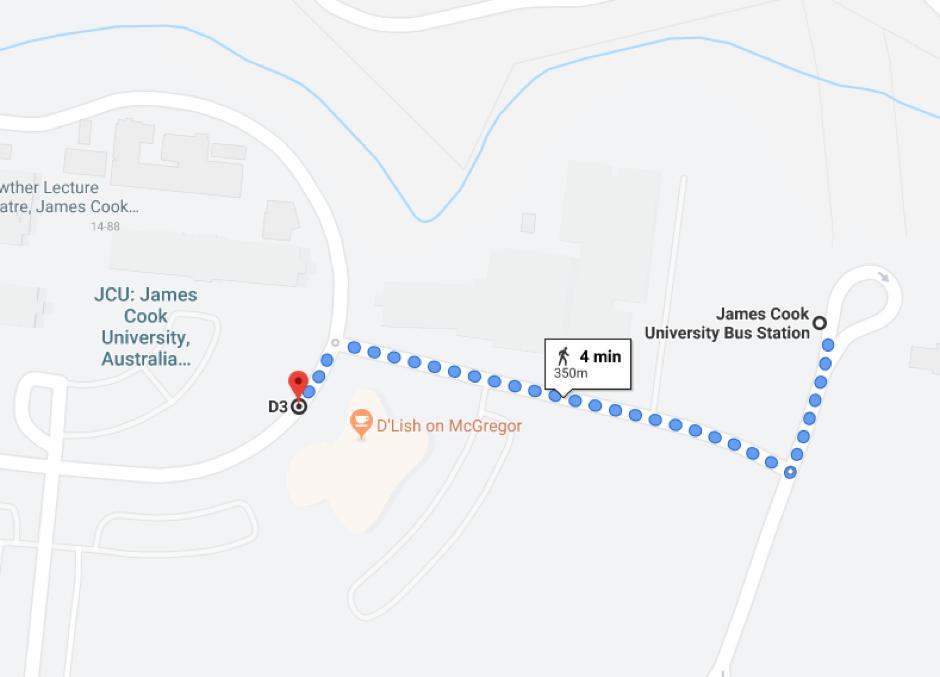
For those who take bus from the Cairns CBD to the campus, you can get off at the James Cook University Bus Station and walk to the venue for just 4 minutes.
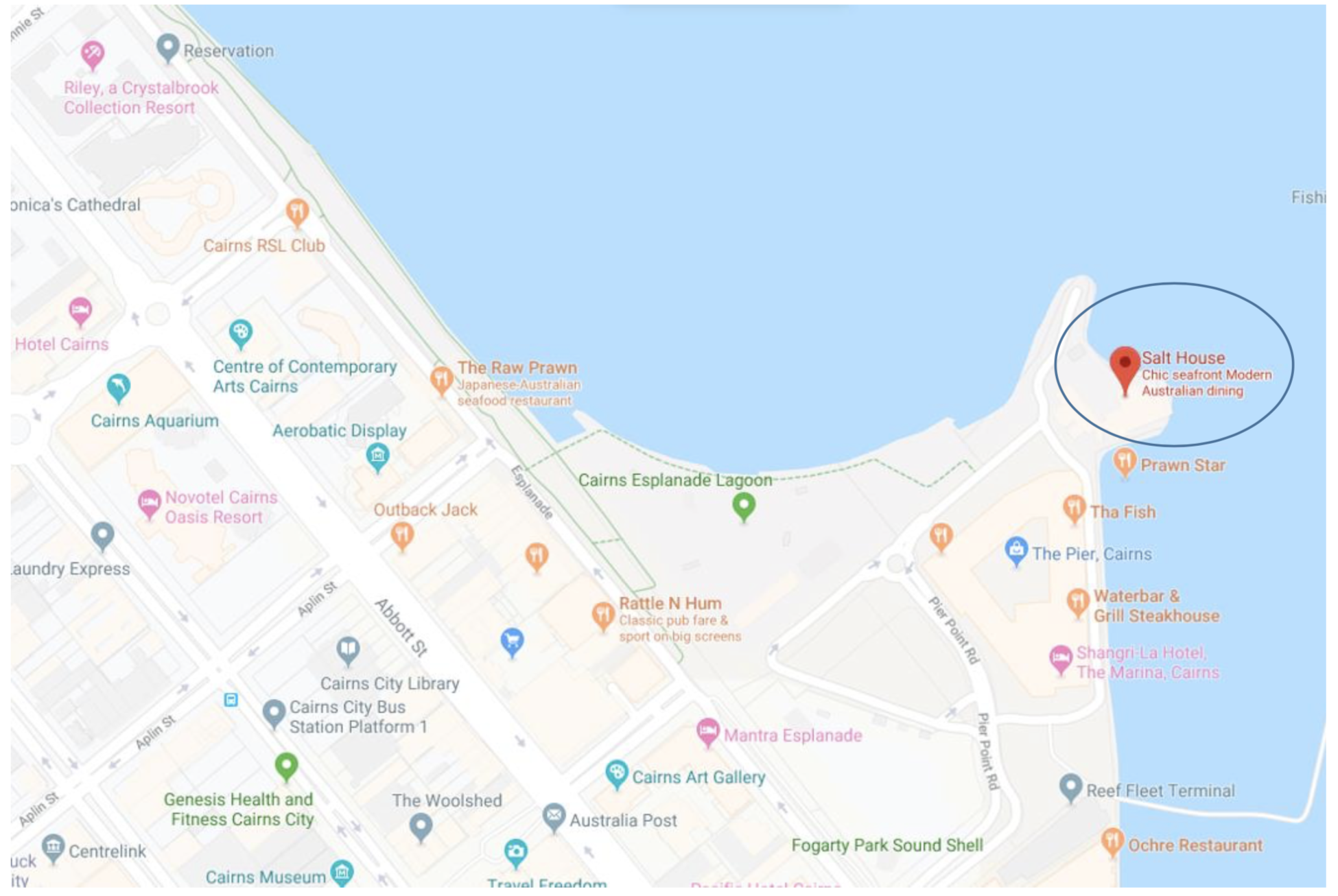
Reception Venue: Salt House
Time: 5pm-7pm on 2nd Oct 2019 (Wed) https://salthouse.com.au/
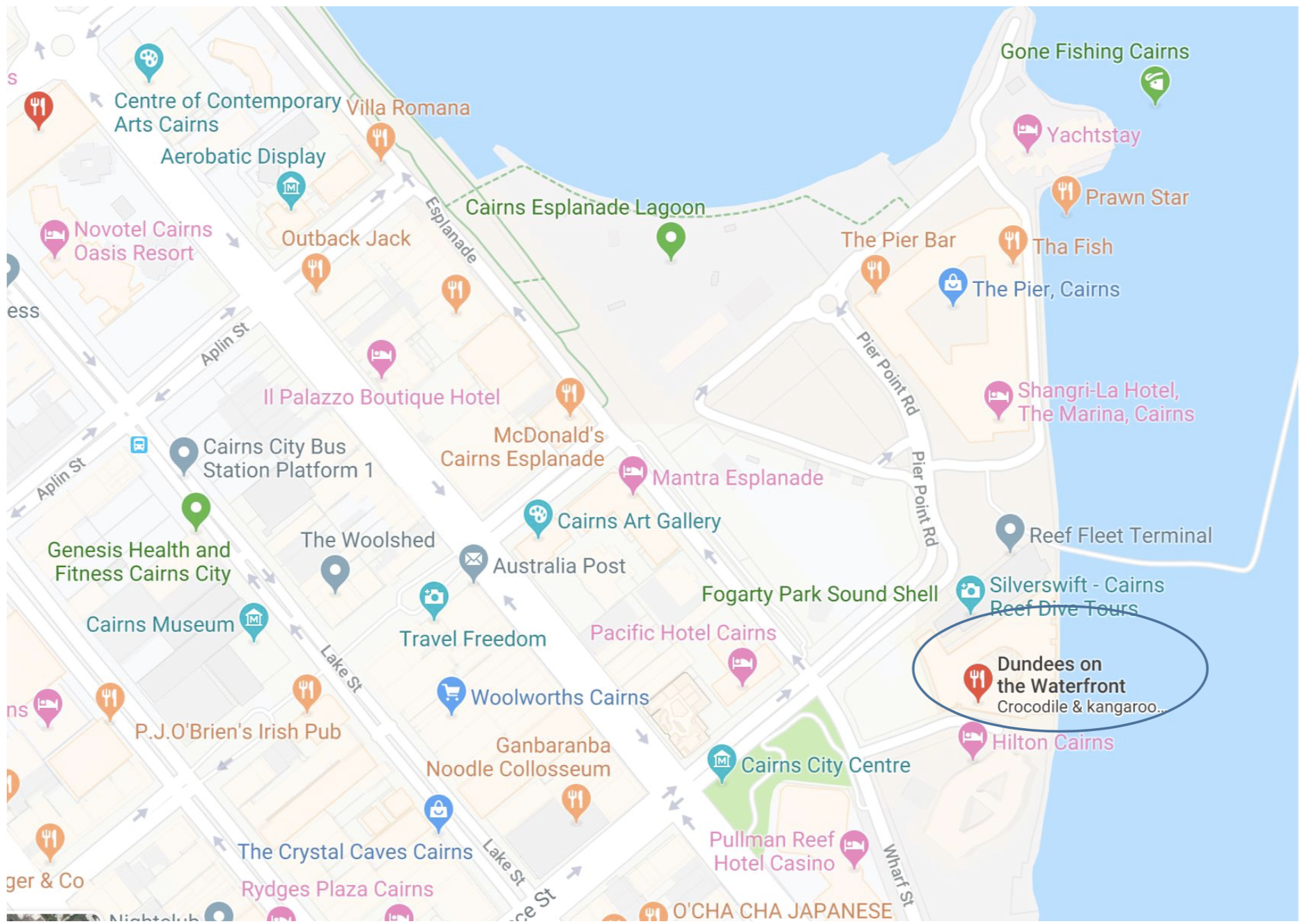
Banquet Venue: Dundee’s Restaurant Waterfront Time: 6pm-9pm on 4th Oct 2019 (Friday)https://www.dundees.com.au/
More details can be found here.
The closest airport is Cairns Airport, which is 15km away from the campus. There are many international direct flights flying to Cairns (e.g. Hong Kong, Shenzhen, Guangzhou, Shanghai, Seoul, Osaka, Tokyo, Singapore, Auckland etc.) Alternatively, you can easily catch a domestic flight from any other major cities in Australia (e.g. Sydney, Melbourne, Brisbane, Perth etc.)